Crowdstrike’s 4QFY26 Earnings: The Data Pipeline Disguised as a Security Company
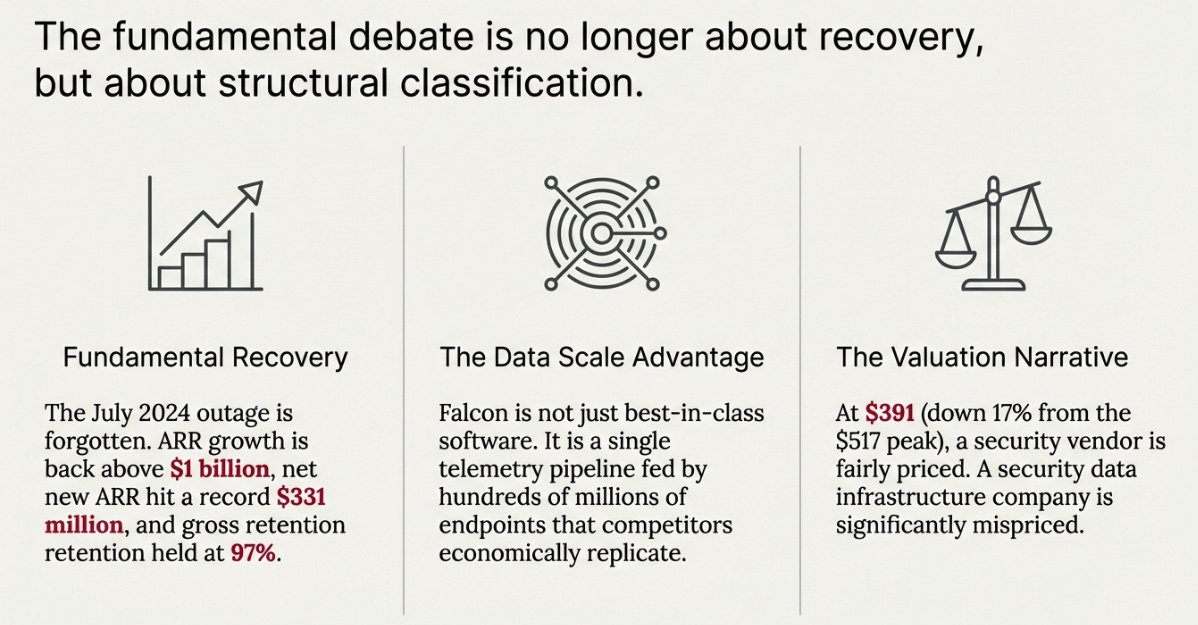
The outage is forgotten, ARR growth is back above $1B, and SIEM is exploding. The real debate now is whether Falcon is just best-in-class security software or the data layer every SOC will run on.
TL;DR
Fundamentals fully recovered: record net new ARR, stable retention, and accelerating platform modules.
Falcon’s advantage is data scale: hundreds of millions of endpoints feeding a single telemetry pipeline competitors can’t replicate.
Valuation depends on the narrative: security vendor = fairly priced; security data infrastructure = significant mispricing.
There are two ways to understand CrowdStrike.
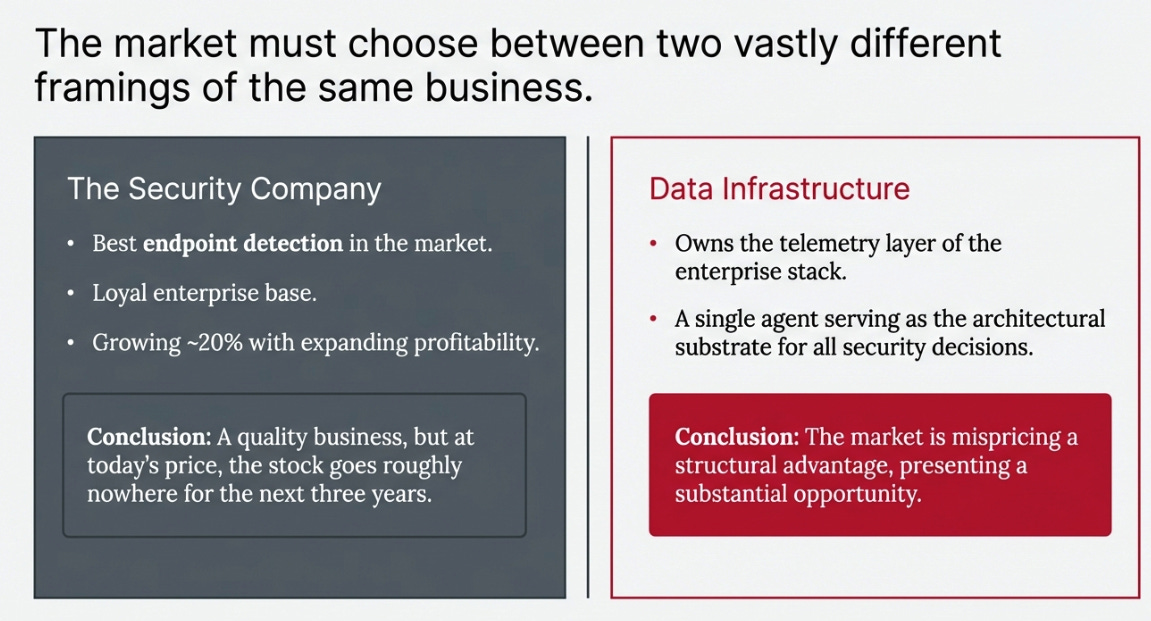
The first version: a very good security company. Best endpoint detection in the market, strong gross margins, loyal enterprise customers who survived the worst IT outage in history and stayed anyway. Growing at roughly 20% with expanding profitability and a platform that is clearly working. A quality business.
The second version: a data infrastructure company that operates inside the security industry. One that owns the telemetry layer of the enterprise security stack, generated by a single agent sitting on hundreds of millions of endpoints, and is becoming the architectural substrate that every other security decision gets made on top of. Not a security product. Infrastructure.
The difference between these two framings is not academic. If the first version is true, CrowdStrike at today’s price is fairly valued and the stock goes roughly nowhere for the next three years. If the second version is true, the market is still pricing a security company and you are looking at a substantial mispricing.
Q4 FY26 did not resolve which version is correct. But it moved the probability toward the second one more decisively than any prior quarter. And there is a specific reason why the dislocation persists, which makes the question worth asking precisely now.
Why Now
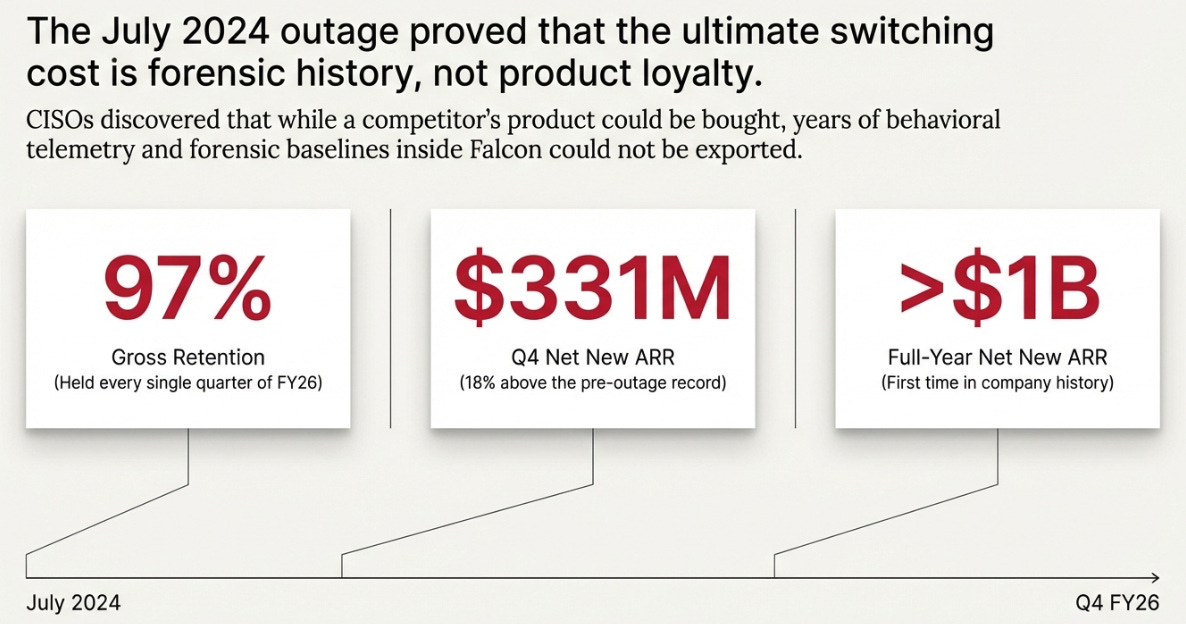
The July 2024 outage created a narrative discount on CrowdStrike that was entirely rational at the time. A company that caused a global IT catastrophe deserved skepticism, elevated risk premium, and multiple compression. The question was whether the damage was structural, permanent churn, retention deterioration, competitive displacement, or operational, meaning recoverable.
Four quarters of data have answered that question completely. Gross retention held at 97% every single quarter of FY26. Net new ARR crossed $331 million in Q4, 18% above the pre-outage record. Full-year net new ARR exceeded $1 billion for the first time in company history. The customers who stayed through the worst-case scenario are the stickiest cohort this company will ever have, and they are expanding, not contracting.
The outage proved something most investors read as negative but was actually strongly positive. It proved the switching cost is not about product quality. CISOs who considered leaving discovered that the years of behavioral telemetry inside their Falcon deployment, the forensic baseline that makes post-incident board reporting possible, was not portable. You could buy a competitor’s product. You could not buy your own history.
The fundamentals recovered. The narrative discount did not. At $391, after a 17% year-to-date decline from a $517 peak, the market is still pricing CrowdStrike as if the outage revealed something bad about the business. It revealed something good. That gap is the opportunity, or the trap, depending on which version of CrowdStrike is real.
What I Got Right and What I Missed
My Q3 piece called the 73% net new ARR growth a comp illusion. That was correct. The underlying growth rate was approximately 20%, not 73%, and the right baseline was the pre-outage trend rather than the disaster quarter. I was also right that at $517 and 24x forward revenue there was no margin of safety. The 17% decline since December confirms it.
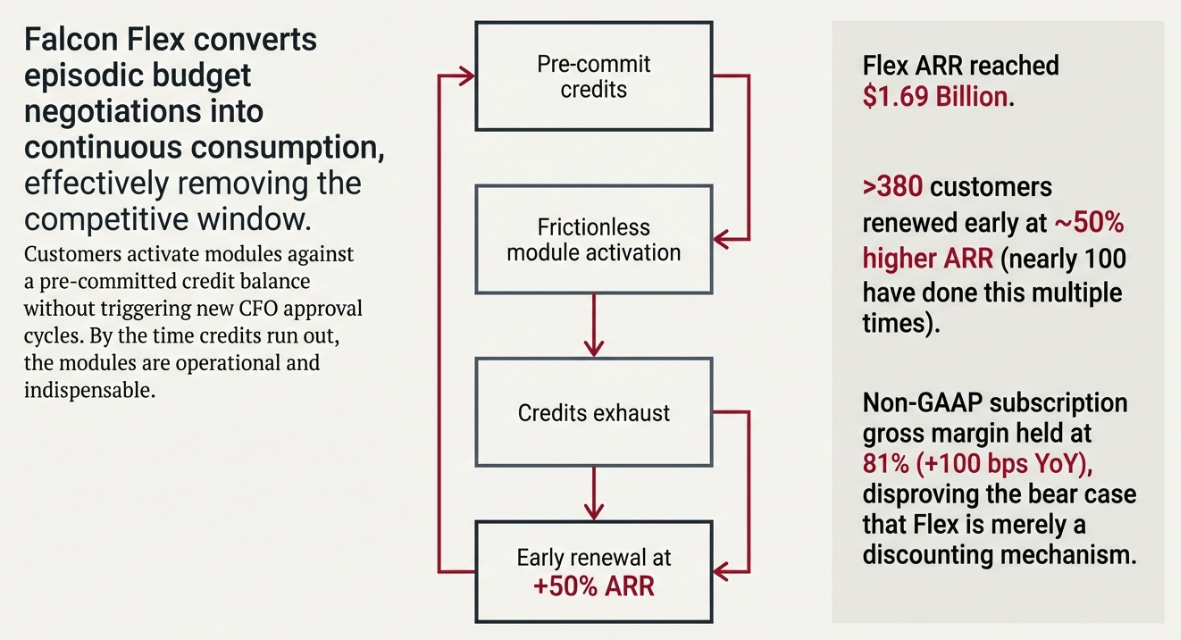
What I missed was the behavioral mechanics of Falcon Flex. I treated the re-Flex statistics as anecdotal color. They were structural evidence. Over 380 customers have returned to renew Flex commitments early, at approximately 50% higher ARR. Nearly 100 have done this multiple times. I knew those numbers and classified them as marketing. I should have classified them as a model change.
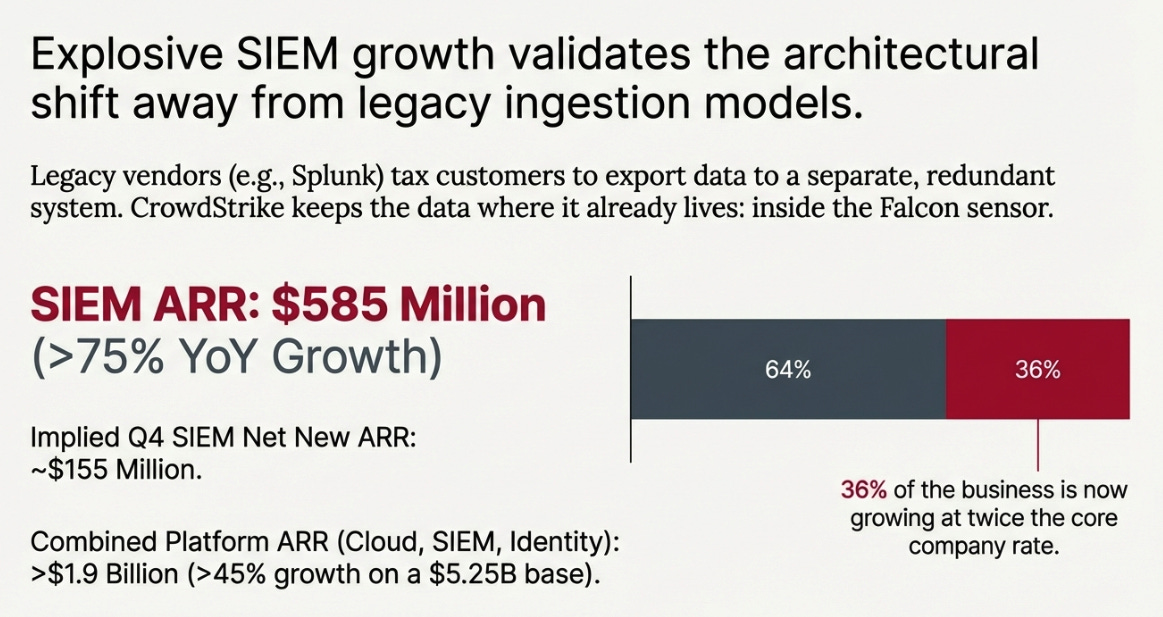
I also misread the SIEM silence. I wrote in Q3 that if SIEM had grown to $600 million, Kurtz would have said so. He said so this quarter, $585 million ARR, growing above 75% year-over-year, with implied Q4 net new ARR of roughly $155 million exceeding any prior full-year figure. The silence in Q3 was strategic, not defensive. Management was waiting for a trend rather than a data point. That is a meaningful distinction and I drew the wrong inference.
The correction matters because it changes the thesis, not just the numbers.
The Central Insight: This Is a Data Pipeline
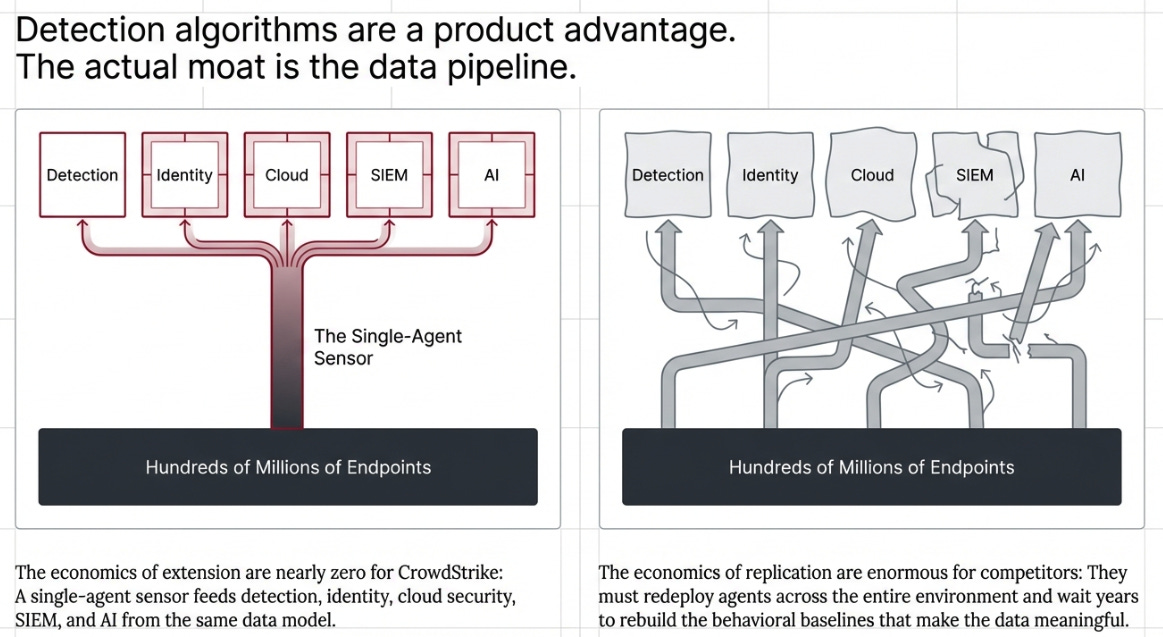
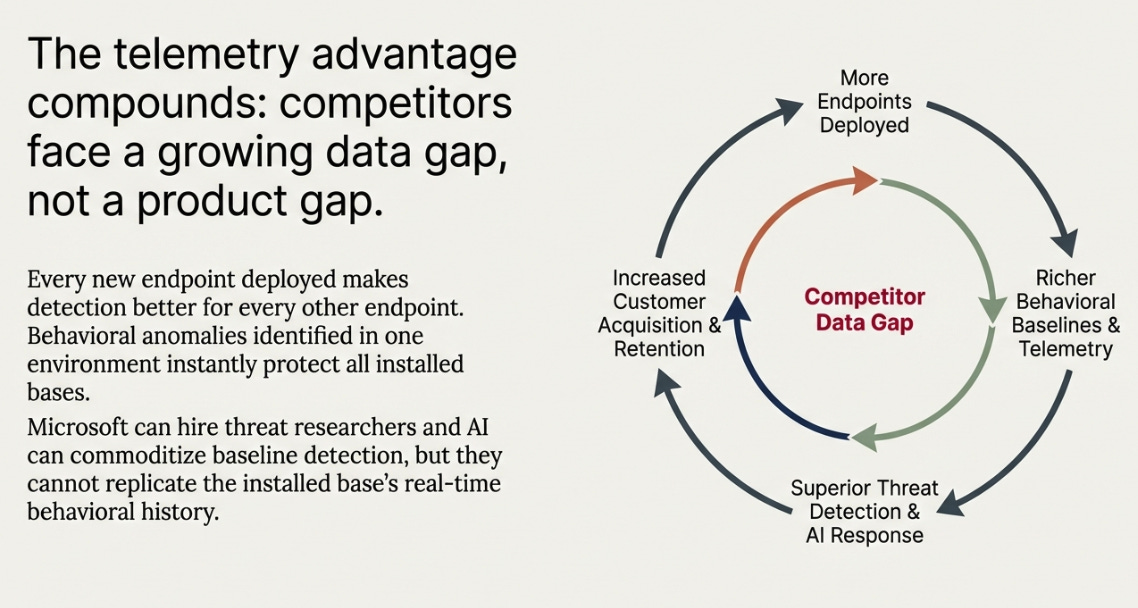
CrowdStrike’s moat is not its detection algorithms. Detection quality is a product advantage, and product advantages erode. Microsoft can hire threat researchers. AI makes baseline detection increasingly commoditized. If the moat were detection, the bear case would be strong and getting stronger.
The actual moat is the data pipeline.
The single-agent sensor on hundreds of millions of endpoints generates telemetry that feeds detection, identity, cloud security, SIEM, and AI-driven response, all from the same data source, in the same data model. Each new module extends this pipeline rather than building a new one. The economics of extension are nearly zero for CrowdStrike. The economics of replication are enormous for a competitor: they would need to redeploy agents across the same environment and then wait years to rebuild behavioral baselines that make the data meaningful.
This is why 97% gross retention held through an event that gave every CISO in the world explicit permission to leave. The switching cost is not “we like the product.” It is “we would lose the forensic history of our environment.” That history does not export. It lives in Falcon.
Here is what makes this moat compound rather than simply persist: every new endpoint Falcon deploys to makes detection better for every other endpoint. Behavioral anomalies are identified across the entire installed base, threats seen in one environment protect all environments. This is not a feature advantage that competitors can hire engineers to match. It is a data advantage that widens as CrowdStrike grows. The more endpoints, the better the detection. The better the detection, the more endpoints. Competitors do not face a product gap. They face a data gap that grows larger every quarter CrowdStrike adds customers.
SIEM makes this architecture visible. Legacy vendors like Splunk built their business around ingesting data from everywhere expensively, charging by volume, effectively taxing customers for the privilege of their own data. CrowdStrike’s argument is that this model is backwards. The most valuable security telemetry already lives inside the Falcon sensor. The security operations center’s data plane does not need to export to a separate system. The separate system is redundant. You already have the data.
At $585 million ARR growing above 75%, with implied Q4 net new ARR exceeding any prior full-year figure, the market is beginning to validate this architecture. Combined platform ARR, Cloud Security, SIEM, Identity, exceeded $1.9 billion, growing above 45% on a $5.25 billion base. Thirty-six percent of the business is growing at twice the company rate. The adjacencies are no longer adjacencies. They are the growth engine, and they are growing faster than the core.
Falcon Flex: The Behavioral Proof
Flex converts enterprise security procurement from episodic budget negotiations into continuous consumption. Customers pre-commit a credit balance, deploy modules by activating them against that balance without triggering new CFO approval cycles, and when the credits run out, return at higher commitments because the modules are now operational and indispensable.
Over 380 customers have renewed early at approximately 50% higher ARR. Nearly 100 have done this multiple times. Flex ARR reached $1.69 billion while non-GAAP subscription gross margin held at 81%, up 100 basis points year-over-year as Flex became a larger share of the base. The bear case that Flex was a discounting mechanism has no data support. Margins expanded as Flex scaled.
What Flex actually does is remove the competitive window. You cannot undercut a deployed module with a cheaper alternative when the deployment decision has already been made and the budget has already been committed. The question is no longer what to buy. It is what to activate next.
The unit economics remain opaque. Management emphasizes behavioral metrics, renewal rates, credit consumption velocity, ARR uplift, over cohort-level detail. This is a choice. Companies disclose what proves their case and omit what complicates it. The margin expansion as Flex scales suggests the economics are favorable; the absence of cohort-level disclosure suggests they are not uniformly favorable across all customer segments. The bet is that aggregate economics dominate the edge cases. That bet looks good today. It requires monitoring.
The metric I want disclosed and isn’t yet: Re-Flex cycle cadence. Whether successive cohorts are burning through credits faster and returning sooner is the earliest leading indicator of flywheel acceleration versus plateau. Ask for it on the Q1 call.
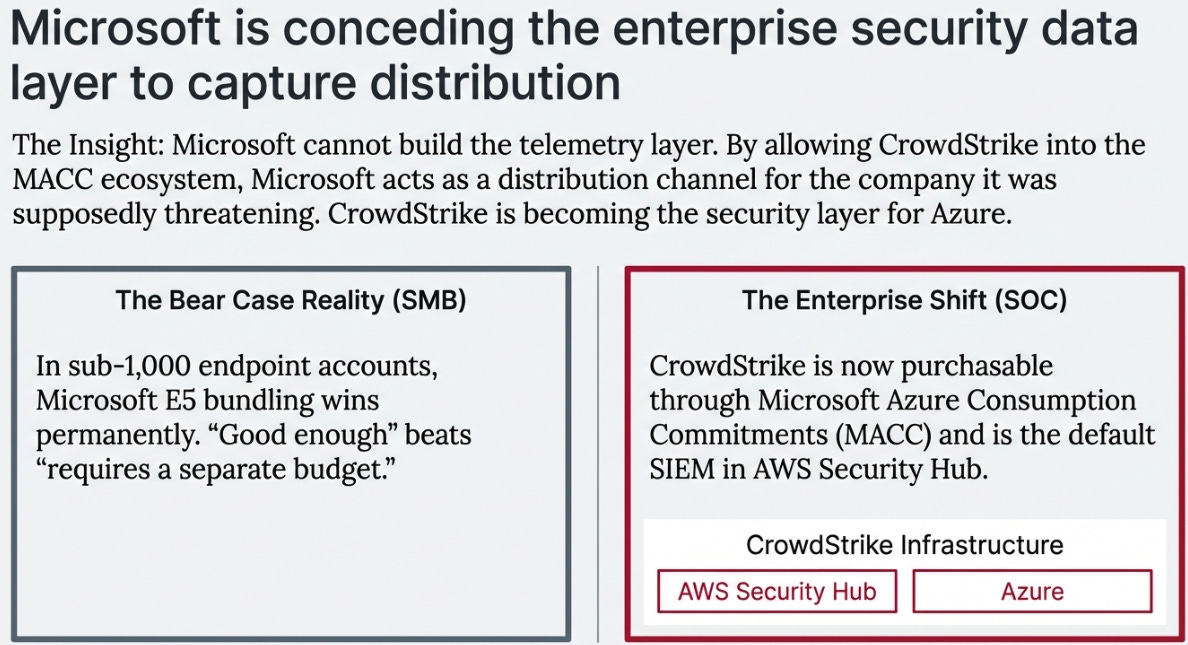
Microsoft: Concession, Not Competition
The standard bear case on Microsoft is structurally correct in one segment and wrong in the one that matters more.
In sub-1,000 endpoint accounts, SMB, lower mid-market, E5 bundling wins. “Good enough plus already paying for it” beats “demonstrably better but requires a separate budget line.” That dynamic is real and probably permanent.
In the enterprise SOC, something different happened this quarter.
CrowdStrike is now purchasable through Microsoft Azure Consumption Commitments. AWS has designated Falcon as the default SIEM in Security Hub. The two largest hyperscalers have both entered structural partnerships with CrowdStrike simultaneously, one giving it access to Azure’s enterprise budget infrastructure, one making it the default security data layer in the world’s largest cloud.
The question worth sitting with: why would Microsoft allow a competitor to ride its consumption commitment framework? The answer is that Microsoft cannot build the telemetry layer. Years of behavioral data across millions of endpoints in specific customer environments is not replicable at any speed or cost that makes strategic sense. By allowing CrowdStrike into the MACC ecosystem, Microsoft is conceding the security data infrastructure layer and capturing the distribution relationship instead. That is not a channel deal. That is a category boundary being drawn.
CrowdStrike is becoming the security layer for Azure, not the alternative to it. The budget infrastructure Microsoft built to consolidate enterprise spend is now a distribution channel for the company Microsoft was supposedly threatening.
The test is Q1 and Q2 FY27 commentary. If CrowdStrike names MACC-attributed mid-market wins, the dynamic is real. If the partnership is never mentioned again, it was a press release.
Variant Perception
The market at $391 has repriced CrowdStrike from momentum compounder to quality at fair value. A record quarter produces essentially no stock reaction because fair value is already embedded in the price. Two things are not embedded.
The normalized margin story. CrowdStrike’s reported FY26 non-GAAP operating margin was 22%. Inside that number: $117.7 million in July 19 incident costs and $44.8 million in strategic plan charges, together about three and a half percentage points of temporary cost that disappears mechanically in FY27. You are not buying a 22% margin business at $391. You are buying a 25-26% margin business carrying costs the income statement is still absorbing. That gap closes in four quarters with no execution required.
The architecture reclassification. ServiceNow spent three years being valued as an ITSM tool before the market reclassified it as an enterprise workflow operating system. The multiple re-rated significantly on that reclassification alone, with no fundamental change in the business. The SIEM number this quarter is the first piece of evidence the market needs for the equivalent reclassification on CrowdStrike, from security product company to security data infrastructure. It is not yet sufficient evidence. One or two more quarters of SIEM confirmation, combined with named hyperscaler-attributed wins, would likely be sufficient.
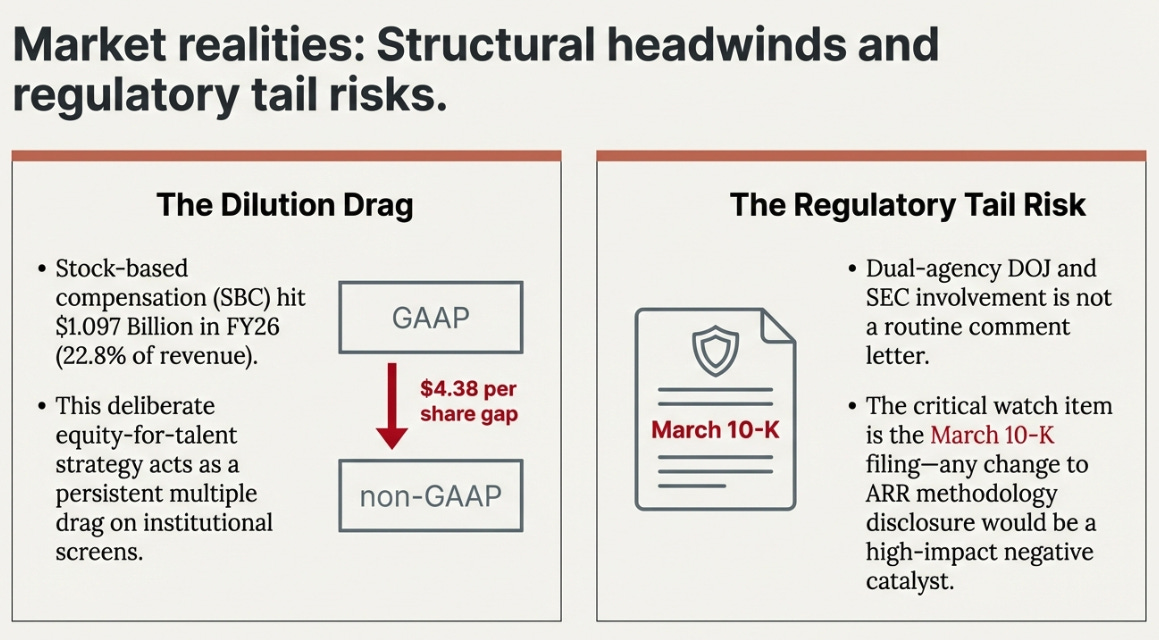
What the market may be correctly pricing: the SBC structural headwind. Stock-based compensation was $1.097 billion in FY26, 22.8% of revenue, growing faster than revenue, creating a $4.38 per share gap between GAAP and non-GAAP earnings. CrowdStrike is making a deliberate choice to pay for talent in equity rather than cash. That preserves cash flow but dilutes shareholders and creates a widening GAAP loss that institutional screens will increasingly penalize. This is a known trade-off. It is a persistent drag on the multiple independent of fundamental performance.
The regulatory inquiry is the tail risk. Dual-agency DOJ and SEC involvement is categorically different from a routine comment letter. The 10-K filing in March is the first real read on whether the language normalizes or escalates. An ARR methodology disclosure change, even a small one, would be the highest-impact negative catalyst available to this stock right now.
Three Years: Three Honest Scenarios
Bull case: approximately $650, 19% annualized return.
SIEM reaches $1.5 billion ARR through confirmed Splunk and Sentinel displacements rather than greenfield alone. MACC partnership generates named mid-market wins by Q3 FY27. Flex proves margin-neutral or better at 40% of total ARR. Charlotte AI becomes a genuine new pricing tier. The market executes the reclassification, from security software to security data infrastructure, and the multiple re-rates accordingly.
Revenue CAGR FY26-29: 24-25%. FCF margin: 36-38%. Exit multiple: 38-40x FY29 FCF.
Base case: approximately $390-420, essentially zero return.
Platform consolidation continues, SIEM grows but stays a module rather than a disclosed platform pillar until FY28, Flex remains margin-neutral without expanding gross margin, and the multiple holds where it is. The base case is already priced at $391. Buying here in the base scenario produces no return for three years. That is the actual risk, not catastrophic loss but three years of opportunity cost.
Revenue CAGR: 19-20%. FCF margin: 32-34%. Exit multiple: 30-32x FY29 FCF.
Bear case: approximately $230, -17% annualized.
The bear case does not require CrowdStrike to fail at execution. It requires winning the architecture battle and losing the economics.
Here is what that looks like: SIEM becomes the default SOC standard, Microsoft responds by building a comparable telemetry layer into Sentinel over three years, and distributes it to E5 customers at zero marginal cost. CrowdStrike ends up with superior technology in a market that has stopped paying for superiority. The data pipeline is real. The pricing power is not. Meanwhile a regulatory disclosure requires an ARR methodology change, even a 3-4% retroactive revision impairs the growth narrative the entire bull thesis is anchored to, and the multiple compresses from 30x to 22x FCF as the platform premium evaporates.
Revenue CAGR: 14-15%. FCF margin: 28-30%. Exit multiple: 22-25x FY29 FCF. The company survives and generates cash. The stock loses badly.
What To Track
Six questions resolve the thesis over the next 18 months.
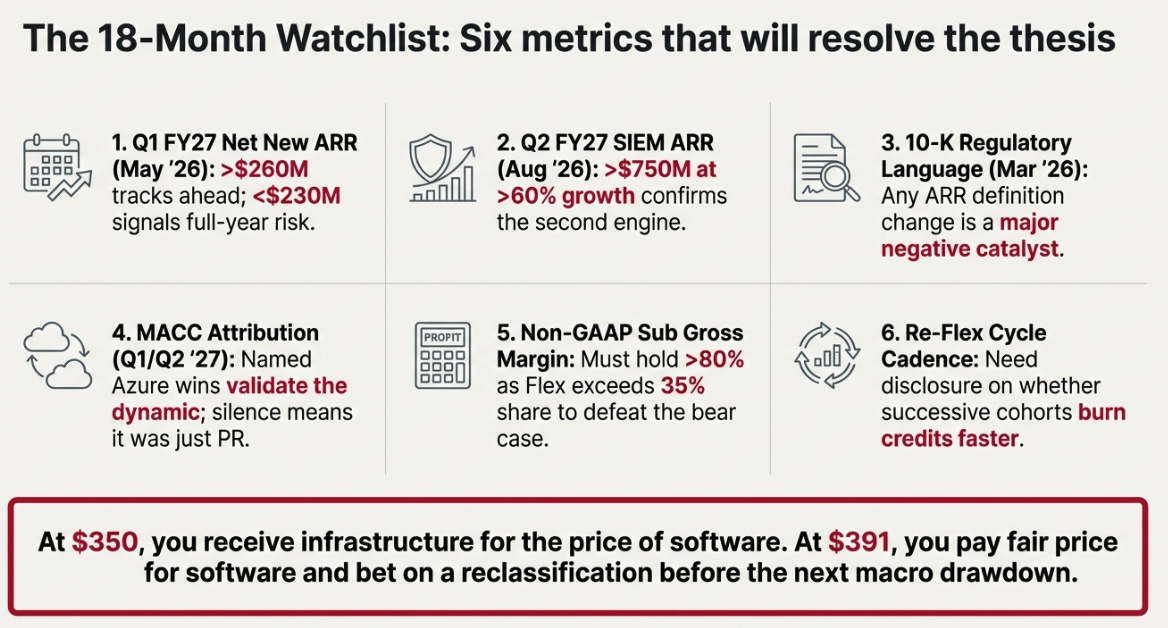
Q1 FY27 net new ARR, May 2026. Above $260 million means FY27 is tracking ahead. Below $230 million means the full-year ARR guide is at risk and Q4 was partially seasonal. This is the single most important data point in the next six months.
SIEM ARR at Q2 FY27, August 2026. Above $750 million at sustained growth above 60% confirms the second engine. Below $620 million means Q4 was a timed disclosure, not a trend. Named Splunk or Sentinel displacement wins outweigh ten greenfield deployments for thesis purposes. Composition tells you more than the aggregate.
10-K regulatory language, March 2026. Compare it word-for-word to the prior filing. Any change in ARR definition, escalation in inquiry description, or new revenue recognition language is the highest-impact near-term negative catalyst.
MACC attribution in Q1 or Q2 FY27 commentary. Named wins through Azure Marketplace reprice the Microsoft dynamic materially. Silence means press release.
Non-GAAP subscription gross margin as Flex scales. Above 80% sustained at 35%+ Flex share closes the economics bear case. Below 79% at that scale requires re-examination of the entire Flex thesis.
Re-Flex cycle cadence, demand this be disclosed. Whether successive cohorts burn through credits faster and return sooner is the earliest leading indicator of flywheel acceleration versus plateau. Not currently disclosed. Ask for it on the Q1 call.
The Updated View
My Q3 view was precise: comp illusion on the NNA headline, no margin of safety at $517. Both correct.
The updated view is equally precise.
At $350, you are paying for a security product company and receiving a data infrastructure company. At $391, you are paying fair price for a security product company and betting the market reclassifies it before the next macro drawdown.
This is a platform option with proof milestones, not a set-and-forget compounder. The milestones, Q1 NNA, SIEM trajectory, 10-K language, arrive within 60 days. Position size should reflect the certainty level, which is meaningful but not complete. The thesis is specific. The falsification conditions are specific. When you know what would make you wrong, you know how much to bet.
Disclaimer:
The content does not constitute any kind of investment or financial advice. Kindly reach out to your advisor for any investment-related advice. Please refer to the tab “Legal | Disclaimer” to read the complete disclaimer.