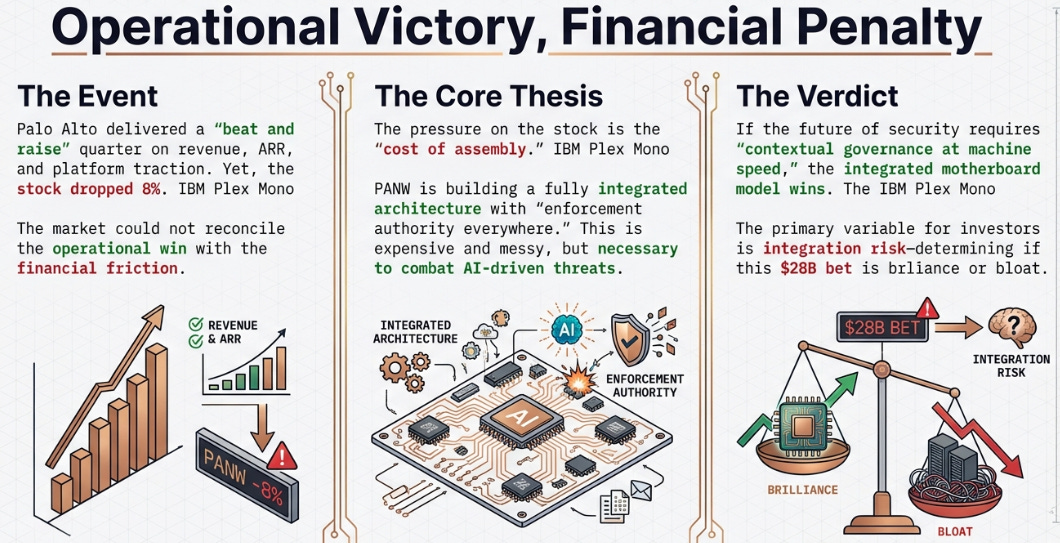
Palo Alto (PANW) 2QFY26 Earnings: Won the Quarter. Lost the Stock.
The friction of fragmentation, integration risk, and why Palo Alto is building the integrated motherboard of cybersecurity.
TL;DR:
Operationally, Palo Alto delivered: ARR growth, XSIAM traction, platform momentum. Financially, margin compression and dilution spooked a 43x multiple.
The pressure is the cost of assembling a fully integrated security architecture with enforcement authority everywhere.
If AI makes security contextual and machine-speed, the integrated “motherboard” wins: but integration risk determines whether that’s brilliance or bloat.
The Paradox
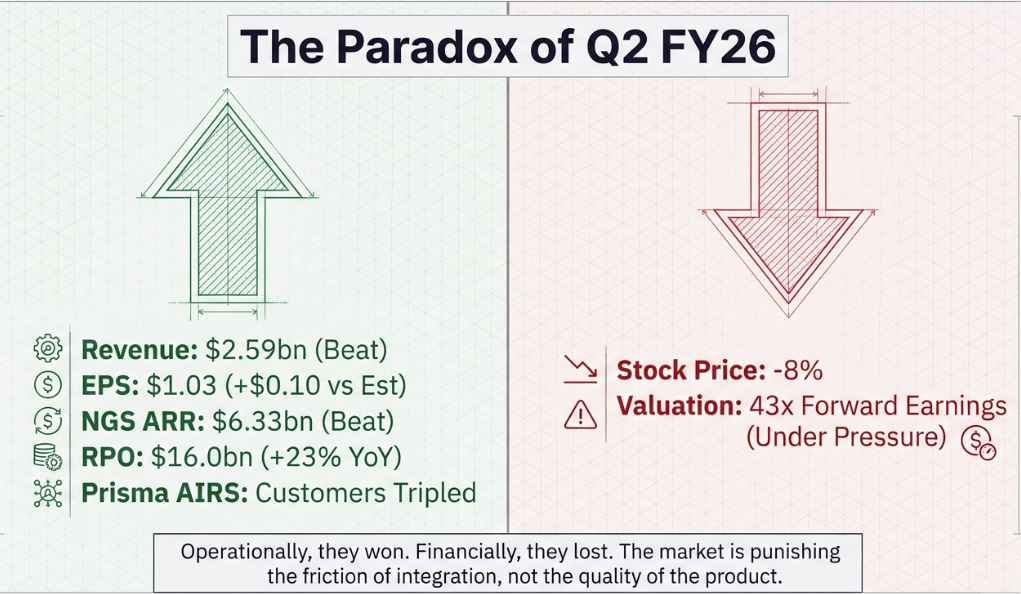
Palo Alto Networks reported fiscal second quarter results that, by any conventional measure, were excellent. Revenue of $2.59 billion beat consensus. Earnings per share of $1.03 crushed the estimate by a dime. Next-Generation Security ARR hit $6.33 billion, blowing past the $6.14 billion estimate. RPO grew 23% to $16.0 billion. SASE crossed $1.5 billion in ARR growing 40%. XSIAM crossed $500 million. Prisma AIRS tripled its customer count to over 100 in a single quarter.
The stock dropped 8%.
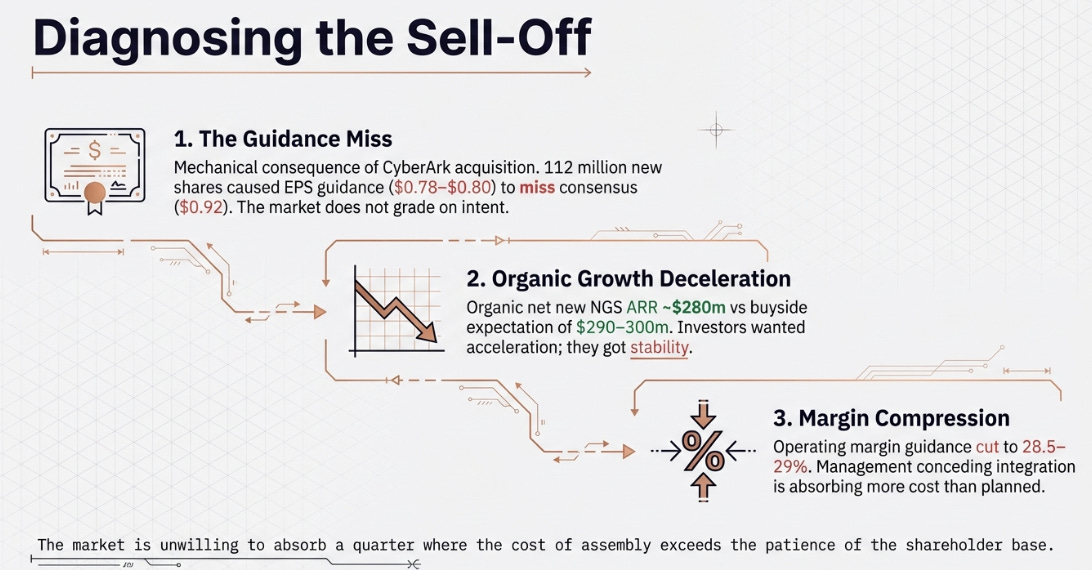
This is the kind of result that makes technology investing humbling. A company delivers its strongest operational quarter in years and the market punishes it. Three numbers underneath the headline beats explain why.
First, third-quarter EPS guidance of $0.78–$0.80 missed consensus of $0.92 by 15%, a mechanical consequence of 112 million new shares from the CyberArk acquisition, but the market does not grade on intent. Second, organic net new NGS ARR of roughly $280 million came in below the buyside’s $290–300 million expectation. The sellside was satisfied; the institutional holders who move the stock were not. They watch the derivative, not the level, and the acceleration they wanted was not there. Third, full-year operating margin guidance was cut from a prior 29.5–30% framework to 28.5–29%. This was not dilution math. This was management conceding the integration is absorbing more cost than planned.
The one-line version: Palo Alto won the operational argument and lost the financial one. At 43 times forward earnings, the market cannot absorb a quarter where the cost of assembly exceeds the patience of the shareholder base. Which raises the question: what is being assembled, and why does it cost this much?
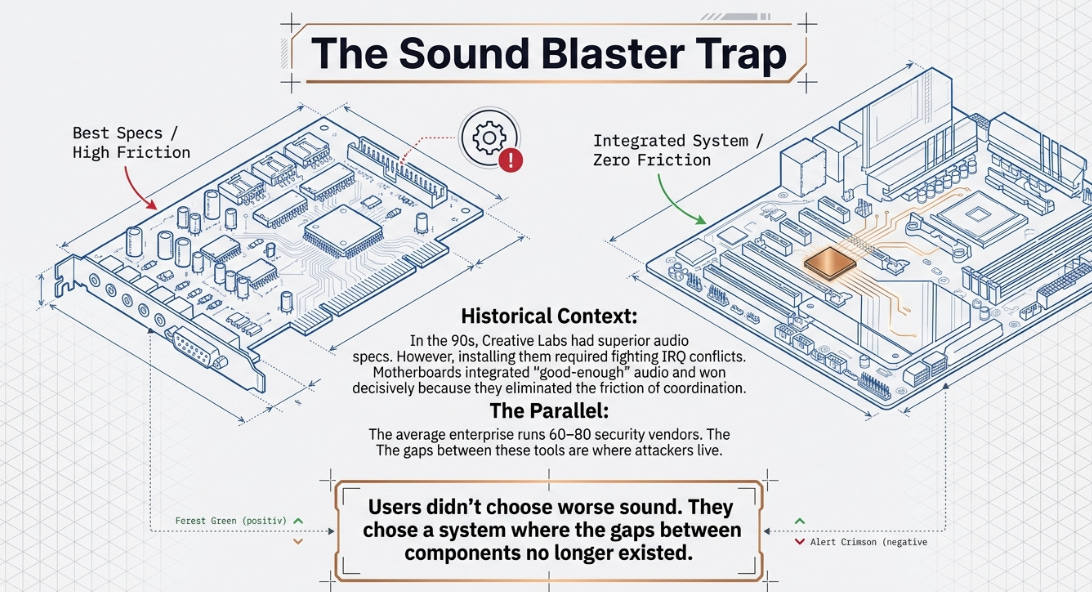
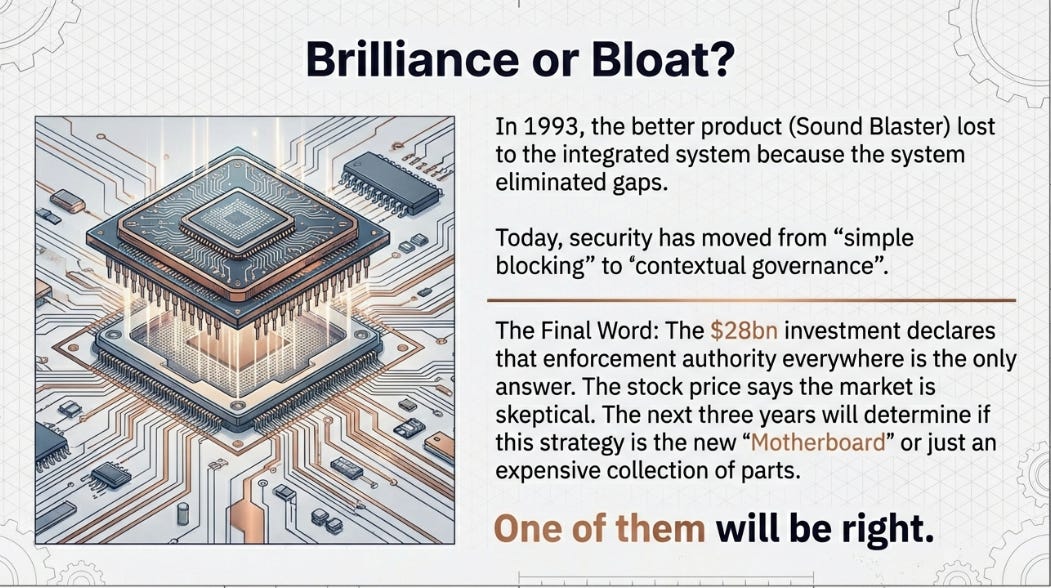
The Sound Blaster Trap
In the early 1990s, Creative Labs’ Sound Blaster was the best audio card in the PC industry. Audiophiles and gamers swore by it. But installing it meant fighting IRQ conflicts, the arcane system by which PC components negotiated access to the processor. Every new peripheral was a potential conflict. Drivers were fragile. The system treated each component as a stranger to every other, and making the best-in-class audio card coexist with the rest of the machine was an exercise in frustration.
Then motherboard manufacturers integrated good-enough audio directly onto the board. The sound was worse on every measurable dimension. Creative Labs should have been fine. Their product was objectively better. They weren’t fine. The integrated audio won decisively, because it eliminated the friction of coordination. Users didn’t choose worse sound. They chose a system where the gaps between the components no longer existed.
The average large enterprise runs 60–80 security products from dozens of vendors. Each generates its own telemetry, its own alerts, its own console. An attack chain crosses identity, endpoint, network, and cloud in sequence, ignoring vendor boundaries entirely. Unit 42 says attacks now move four times faster than a year ago, with data exfiltrated in under an hour in a quarter of cases. The SOC analyst is not losing because the tools are bad. The analyst is losing because the gaps between the tools are where the attacker lives. Defense is fragmented; offense is coordinated.
But here is what makes cybersecurity structurally different from PC audio, and what makes Palo Alto’s bet more consequential than a simple integration story. Every new technology wave doesn’t just add new things to secure. It multiplies the number of gaps between security tools. Cloud didn’t just create “cloud security” as a new category. It doubled the tool count and the seams between them multiplied combinatorially. AI agents are doing the same thing again, except with a twist that changes the nature of the security question itself.
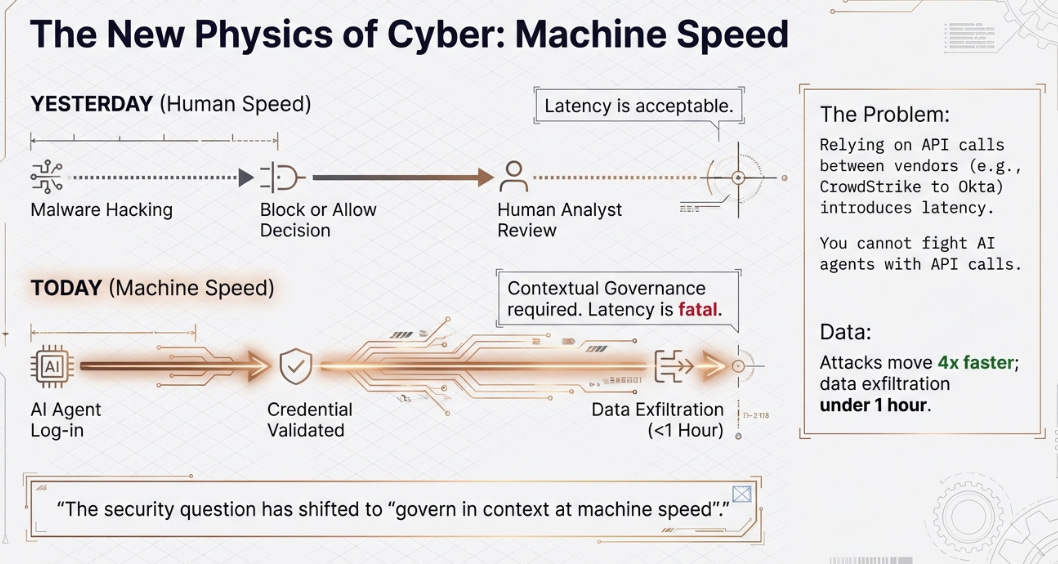
AI agents don’t hack in. They log in. They have credentials, API keys, authorized access. You cannot firewall an authorized user in the traditional sense. You cannot detect malware in a legitimate API call through signature matching alone. The security question is shifting from “is this packet malicious?”, a binary judgment that a single tool at a single point can answer, to “is this AI agent, logged in with marketing credentials, authorized to access the production database at 3 AM and export five gigabytes of data?” That is a contextual judgment that requires simultaneous knowledge of the identity, the network path, the endpoint behavior, and the cloud workload. No single tool has that context. And assembling it via API calls between separate vendors introduces precisely the latency that machine-speed attacks exploit.
AI didn’t shrink the security market any more than it shrank search. It expanded the complexity of the security question from “block or allow” to “govern in context at machine speed”, and only a system with enforcement authority across every control point can answer that question fast enough to matter.
Seven Years of One Bet
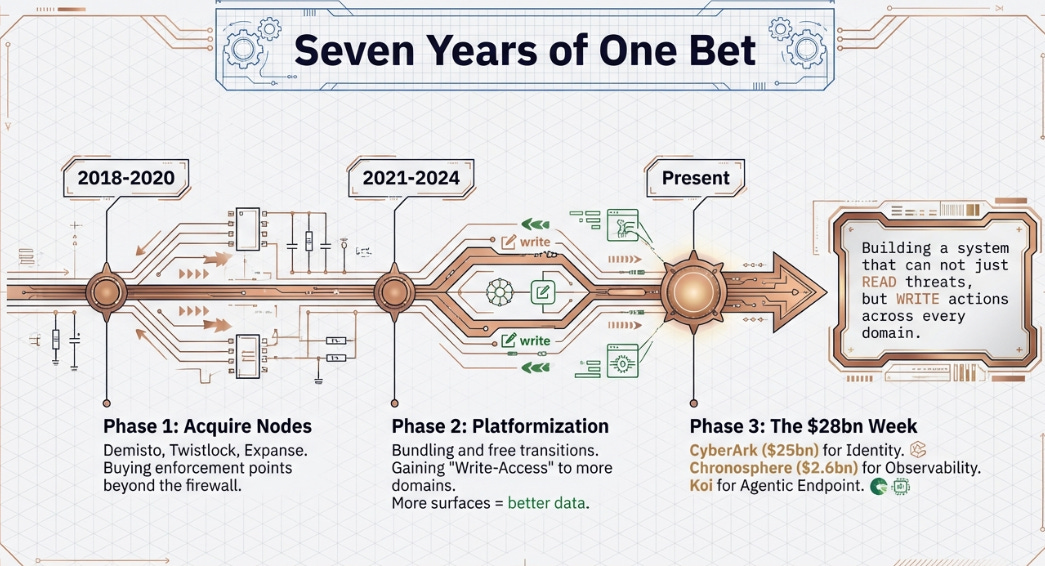
What Nikesh Arora has built since arriving in 2018 looks, in retrospect, like a company methodically acquiring not just products but enforcement authority, the ability to take action, not merely observe, at every control point where that contextual judgment must be made.
First came the acquisition spree, Demisto, Twistlock, CloudGenix, Expanse, read by the market as a legacy firewall vendor panic-buying cloud relevance. The actual logic: Palo Alto was buying enforcement points beyond the dissolving network perimeter. Every acquisition was a node where the system could not just detect a threat but act on it directly.
Then came the controversial pivot to platformization, free transition periods, cannibalized firewall revenue, aggressive bundling. Bears called it desperate discounting. The actual logic: every new enforcement surface generates telemetry that feeds a centralized detection engine, and, crucially, every new node gives the system write-access to another domain. More surfaces, better detection, more places to act, better outcomes, more adoption. This was the compound loop forming, enforce, observe, detect, automate, and the economics looked ugly because building it necessarily preceded operating it.
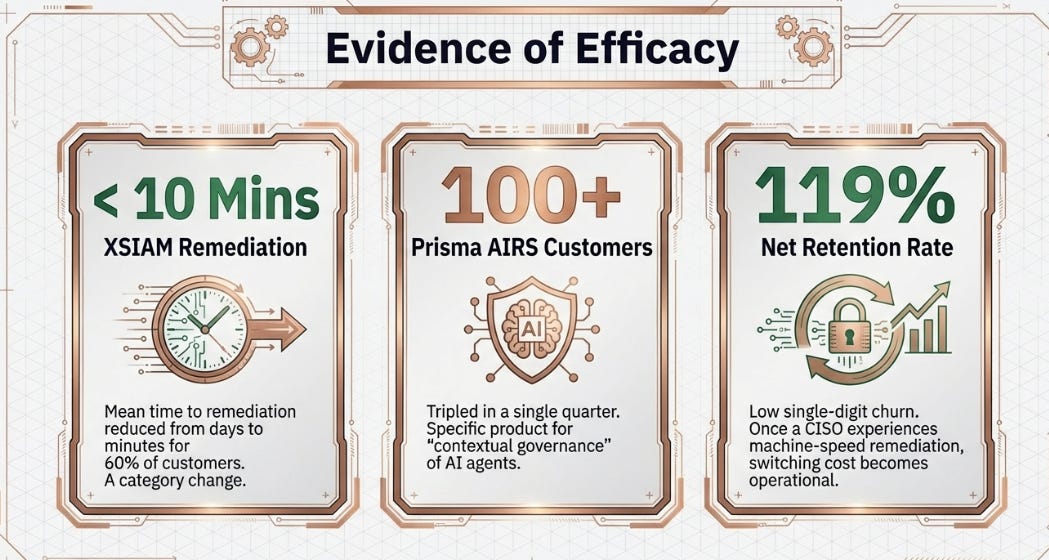
Then XSIAM proved it. An AI-driven SOC ingesting telemetry from all enforcement points, reducing mean time to remediation from days to under ten minutes for over 60% of deployed customers. Not just detecting threats faster. Remediating them, taking action across multiple domains automatically, at machine speed. For organizations that previously measured response in days, this was not an incremental improvement. It was proof that the architecture worked.
The $28 billion week was the thesis reaching its logical conclusion. CyberArk ($25 billion) adds identity, not just another node, but the connective tissue that links every other node. Every network action, every endpoint session, every cloud workload, every AI agent has an identity. By owning identity, Palo Alto doesn’t just add detection in a new domain. It gains the ability to revoke a token, kill a session, or shut down an agent across the entire system. Chronosphere ($2.6 billion) adds observability, what is actually happening across the environment in real time. Koi adds the agentic endpoint, where AI software operates invisible to traditional tools.
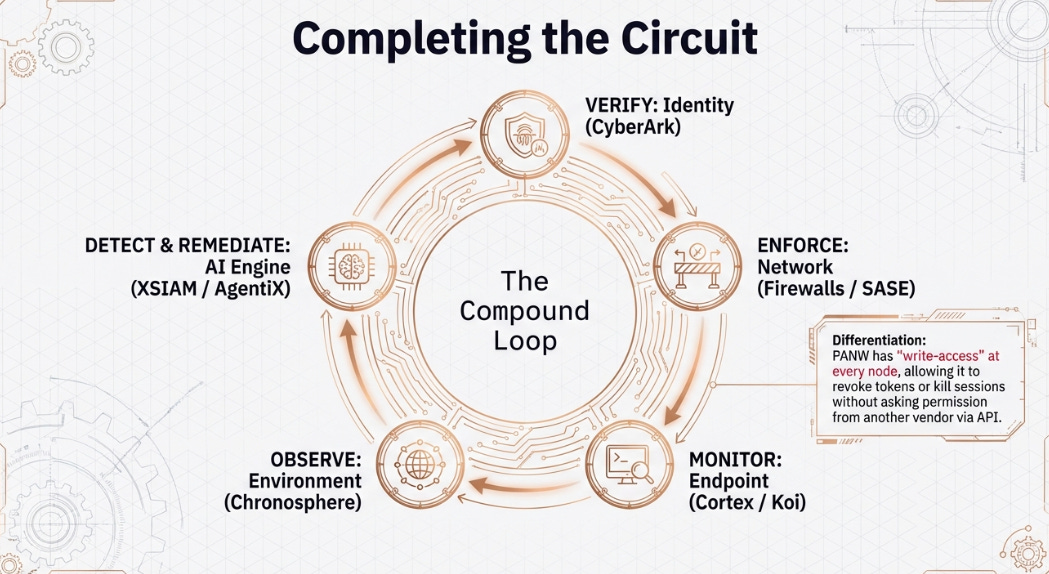
The compound loop is now complete. The system can verify identity (CyberArk), enforce network policy (firewalls, SASE), monitor endpoint behavior (Cortex, Koi), observe the environment (Chronosphere), detect anomalies (XSIAM), and remediate automatically (AgentiX), all with write-access at every node. The contextual governance question, who is this agent, what is it doing, is it authorized, and should we stop it, can now be answered and acted upon in a single integrated system.
Three Architectures
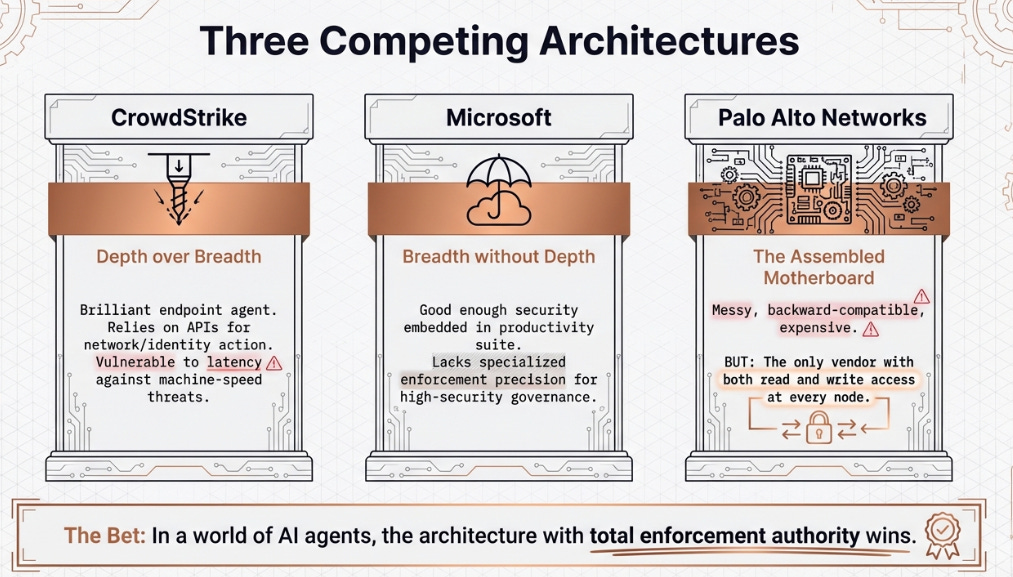
Palo Alto is not competing against a vacuum. Three coherent architectural visions are vying for the enterprise security budget, each with a different answer to the governance question.
CrowdStrike is depth over breadth. Single lightweight agent, nine modules, elegant architecture built from scratch. It sees the endpoint brilliantly and can take action there, but for identity, network, and cloud, it must ask other systems to act via API calls. It can detect the rogue AI agent, but to revoke its credentials or block its network path, it sends a request to Okta or the firewall and waits. That request takes time. At human speed, this is fine. At machine speed, that latency is a vulnerability.
Microsoft is security as a feature of the productivity suite you already own. Defender, Entra, Sentinel, embedded in the identity and collaboration stack with near-universal enterprise adoption. It doesn’t need to be the best. It just needs to be good enough and already installed. The limitation: breadth without depth. Microsoft can see widely but lacks the specialized enforcement and automation to answer contextual governance questions with the precision that high-security environments demand.
Palo Alto is the assembled motherboard. Messy. Backward-compatible. Thirty-plus acquisitions stitched together. But the only vendor with both read-access and write-access at every node, meaning the only one that can answer a contextual security question and enforce the answer across identity, network, endpoint, and cloud simultaneously. The bet: in a world where the security question has become contextual and the time to answer it has collapsed to near-zero, the system with total enforcement authority wins.
All three have structural logic. The question of which wins will be answered over years, by the procurement decisions of thousands of CISOs. But the AI acceleration, the compression of attack timelines to machine speed, structurally favors the architecture with write-access everywhere over the architecture that detects perfectly in one domain and requests action in others.
The Variant Perception
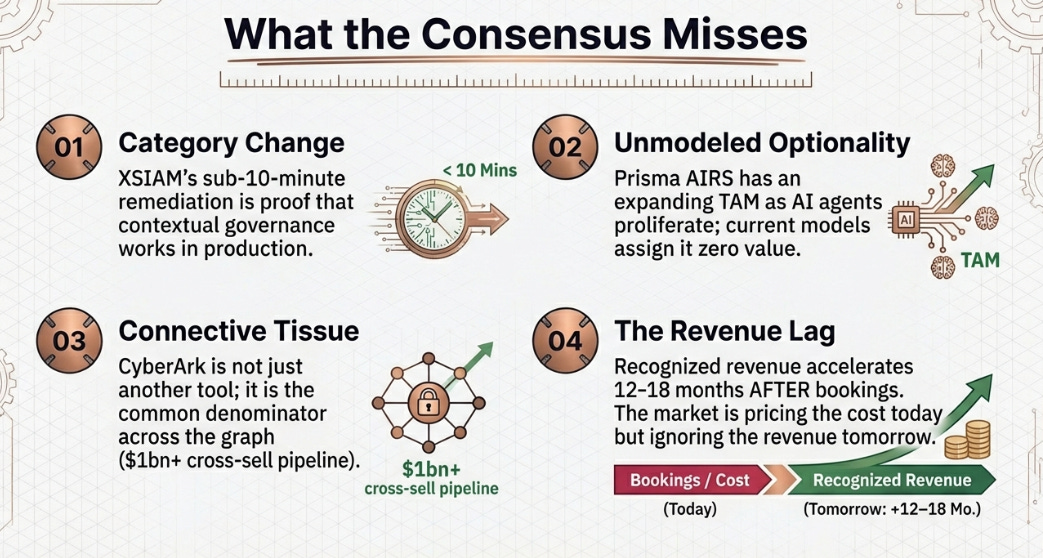
The consensus view is straightforward: operationally strong, strategically sound, too much integration risk at too rich a multiple. Reasonable. Also incomplete.
Four things the consensus is underweighting.
First, XSIAM’s outcome differentiation, sub-ten-minute remediation for 60% of deployed customers, is not a feature advantage but a category change. It is the first proof that contextual governance at machine speed actually works in production. The 119% net retention rate with low single-digit churn among platformized customers confirms that once a CISO experiences it, the switching cost becomes operational, not contractual.
Second, Prisma AIRS represents unmodeled optionality. Over 100 customers, doubled bookings, nine-figure pipeline, trajectory matching XSIAM’s early curve, which became a $500 million business in 3.5 years. No sellside model assigns explicit value because there is no disclosed revenue line. But as AI agents proliferate and the contextual governance question becomes the central challenge for every enterprise, the product addressing that question directly has a TAM that is expanding, not static.
Third, CyberArk at $1.2 billion ARR growing 30% is not just another node, it is the common denominator across the entire graph. The $1 billion-plus cross-sell opportunity into 65,000 firewall customers for certificate lifecycle management is concrete pipeline. The risk: the Day-2 headcount cut of 10%, whether those cuts hit quota-carriers or back-office determines if growth sustains.
Fourth, the ARR-to-revenue conversion lag. At $6.33 billion of NGS ARR growing 28% organically, the recognized revenue acceleration arrives in twelve to eighteen months, precisely as integration costs peak and roll off. The market is pricing the cost today without discounting the revenue tomorrow.
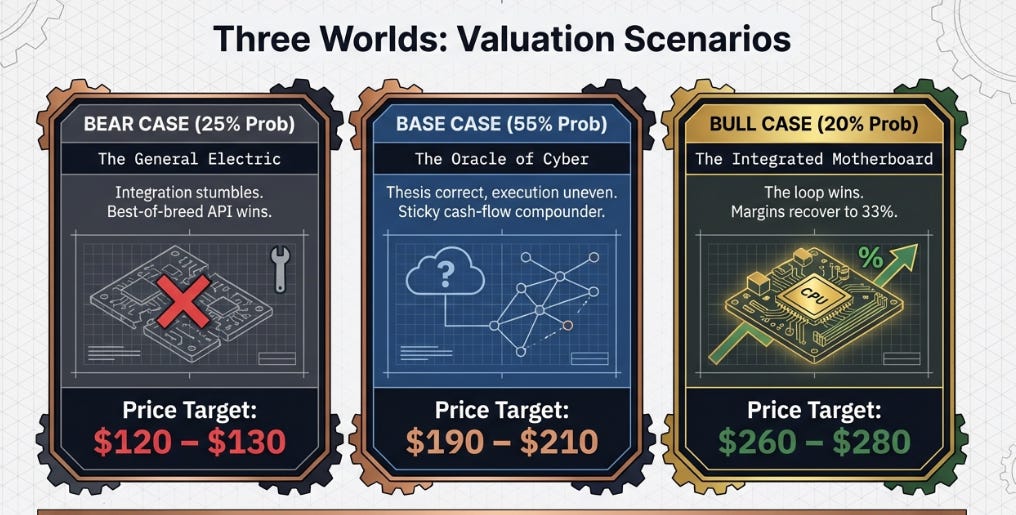
Three Prices, Three Worlds
Bull: “The Integrated Motherboard” ($260–$280). The compound loop wins. Enterprises consolidate security spending as the contextual governance model proves superior. CyberArk sustains 25%+ growth. Prisma AIRS reaches $500 million-plus ARR by FY2028. Revenue compounds at 18–20% to $15–16 billion by FY2029. Margins recover to 32–33%. EPS power of $7-plus at 35–38 times. Probability: ~20%. Requires near-flawless integration across three simultaneous acquisitions.
Base: “The Oracle of Cyber” ($190–$210). Thesis correct, execution uneven. CyberArk decelerates to low-20s growth as GTM alignment takes longer than planned. Revenue at 12–14% CAGR to $13.5–14.5 billion. Margins at 30–31%. EPS of $5.50–$6.00 at 33–35 times. Palo Alto becomes a sticky, high-cash-flow compounder, respected, no longer exciting. Probability: ~55%. Still 20–30% above today.
Bear: “The General Electric” ($120–$130). Integration stumbles. CISOs reject consolidation, preferring best-of-breed assembled via APIs, betting that API latency is manageable even at machine speed. CrowdStrike and Zscaler pick off frustrated customers. Growth decelerates to high single digits. Margins compress to 26–27%. EPS of ~$4.50 at 28–30 times. Probability: ~25%. Requires active deterioration, not merely underwhelming results.
Attractive, not compelling, the right entry for patient capital, not for momentum.
What to Watch
Five signals that resolve the debate.
CyberArk identity ARR growth, next two quarters. Above 25% means the GTM engine works and the connective tissue thesis holds. Below 20% means the most expensive cybersecurity acquisition in history is underperforming standalone.
Operating margin, H1 FY2027. Recovery to 30% or above means the integration costs were transitory. Still below 29% a year from now means the cost structure is permanently heavier than advertised.
Prisma AIRS adoption. From 100 to 250–300 customers within twelve months means the contextual governance question is generating real demand. Stalling below 200 means it remains a narrative without a market.
Platformization renewal economics, H2 FY2027. The 119% NRR is the strongest proof point for the compound loop. But many customers remain in initial promotional terms. The first large-scale renewal cycle reveals whether stickiness is structural or incentive-driven. This is the most important data point that does not yet exist.
Organic net new NGS ARR. The $280 million Q2 print against buyside expectations of $290–300 million is a yellow flag. Two consecutive misses would signal the flywheel is decelerating under integration weight, and that reprices every scenario.
Conclusion
In 1993, Creative Labs had the best audio hardware in the PC industry and a loyal installed base that would argue its superiority in any product comparison. The integrated motherboard had worse specs on every measurable dimension. Creative Labs does not exist as a meaningful company anymore. The integrated solution won, not because it was better at sound, but because it eliminated the gaps where the system broke down.
The security question used to be simple enough that a single tool at a single point could answer it: block or allow. AI has made that question contextual, requiring simultaneous knowledge of identity, network, endpoint, and cloud, and compressed the time to answer it to near-zero. Whether Palo Alto Networks has built the system capable of answering that question, or merely assembled an expensive collection of parts, is what the next three years will determine. The $28 billion says Arora believes the answer requires enforcement authority everywhere, not just detection excellence somewhere. The stock price says the market isn’t sure yet. One of them will be right.
Disclaimer:
The content does not constitute any kind of investment or financial advice. Kindly reach out to your advisor for any investment-related advice. Please refer to the tab “Legal | Disclaimer” to read the complete disclaimer.